We don’t have a useful quantum computer yet, but we do have quantum algorithms. Shor’s algorithm has the potential to factor large numbers faster than otherwise possible, which—if the run times are actually feasible—could break both the RSA and Diffie-Hellman public-key algorithms. Now, computer scientist Oded Regev has a significant speed-up to Shor’s algorithm, at … Read More “Improving Shor’s Algorithm” »
Category: Uncategorized
Auto Added by WPeMatico
Kaspersky researchers are detailing “an attack that over four years backdoored dozens if not thousands of iPhones, many of which belonged to employees of Moscow-based security firm Kaspersky.” It’s a zero-click exploit that makes use of four iPhone zero-days. The most intriguing new detail is the targeting of the heretofore-unknown hardware feature, which proved to … Read More “New iPhone Exploit Uses Four Zero-Days” »
A helpful summary of which US retail stores are using facial recognition, thinking about using it, or currently not planning on using it. (This, of course, can all change without notice.) Three years ago, I wrote that campaigns to ban facial recognition are too narrow. The problem here is identification, correlation, and then discrimination. There’s … Read More “Facial Recognition Systems in the US” »
TikTok seems to be skewing things in the interests of the Chinese Communist Party. (This is a serious analysis, and the methodology looks sound.) Conclusion: Substantial Differences in Hashtag Ratios Raise Concerns about TikTok’s Impartiality Given the research above, we assess a strong possibility that content on TikTok is either amplified or suppressed based on … Read More “TikTok Editorial Analysis” »
They’re short unique strings: Sqids (pronounced “squids”) is an open-source library that lets you generate YouTube-looking IDs from numbers. These IDs are short, can be generated from a custom alphabet and are guaranteed to be collision-free. I haven’t dug into the details enough to know how they can be guaranteed to be collision-free. As usual, … Read More “Friday Squid Blogging: Sqids” »
Wow: To test PIGEON’s performance, I gave it five personal photos from a trip I took across America years ago, none of which have been published online. Some photos were snapped in cities, but a few were taken in places nowhere near roads or other easily recognizable landmarks. That didn’t seem to matter much. It … Read More “AI Is Scarily Good at Guessing the Location of Random Photos” »
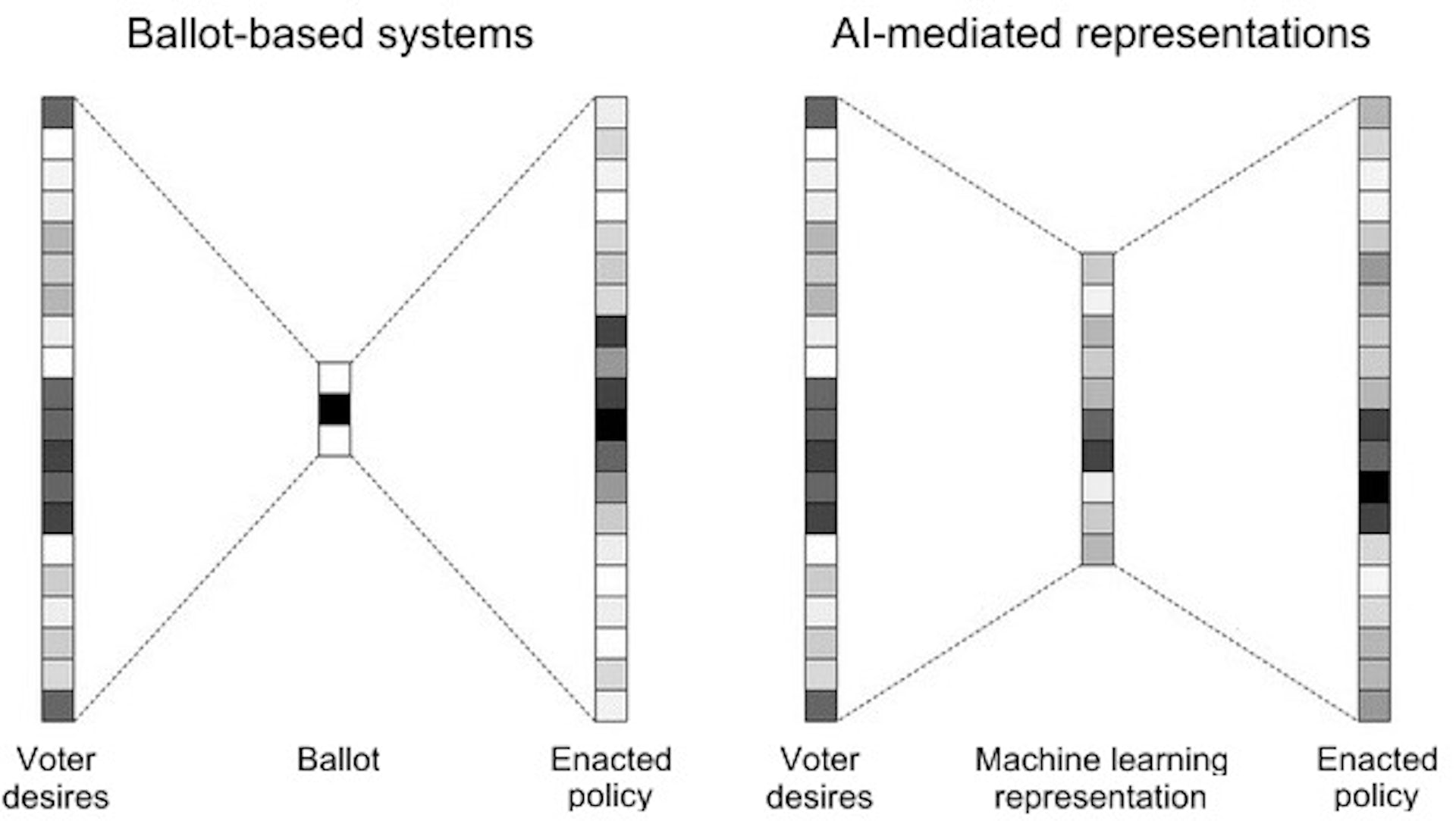
Artificial intelligence is poised to upend much of society, removing human limitations inherent in many systems. One such limitation is information and logistical bottlenecks in decision-making. Traditionally, people have been forced to reduce complex choices to a small handful of options that don’t do justice to their true desires. Artificial intelligence has the potential to … Read More “AI and Lossy Bottlenecks” »
Apple is rolling out a new “Stolen Device Protection” feature that seems well thought out: When Stolen Device Protection is turned on, Face ID or Touch ID authentication is required for additional actions, including viewing passwords or passkeys stored in iCloud Keychain, applying for a new Apple Card, turning off Lost Mode, erasing all content … Read More “New iPhone Security Features to Protect Stolen Devices” »
Google Maps now stores location data locally on your device, meaning that Google no longer has that data to turn over to the police. Powered by WPeMatico
It’s squid parts from college dissections, so it’s not a volume operation. As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered. Read my blog posting guidelines here. Powered by WPeMatico